Learn how each protection module works in GetOverX Shield Next-Generation Security Suite. This documentation provides a visual overview and technical summary of each section.
Purpose: Detects and neutralizes viruses, trojans, and potentially unwanted programs.
Main tools: File Guard, Clean Your PC, File Erase, and Network Hardening.
Scan Mode: Allows manual path selection or full system scanning.
Logs and actions can be reviewed directly from the Scan panel.


Purpose: Reinforces Windows Firewall through policy optimization.
Options: “Booster” to optimize network security and “Reset” to restore default rules.
Advanced Rules: View, enable, or disable custom firewall configurations created by GetOverX.
Purpose: Monitors and blocks suspicious process behavior in real-time.
Activation: Click Activate to enable the protection layer.
Features: Process anomaly detection, alert logging, and advanced rules configuration.


Purpose: Executes untrusted applications in an isolated environment.
Usage: Click Load to safely analyze running programs.
Security: Prevents direct interaction between unknown files and the main system.
Purpose: Continuously monitors endpoints to detect and mitigate cyber threats.
Status: Shows active protection and provides access to logs.
Function: Uses behavioral analytics and process tracking for early anomaly detection.


Remote Access: Manage connections to protected systems.
Log Central: Unified log viewer for all modules.
Services: Manage background processes related to GetOverX Shield.
USB Scan: Quick scan for removable drives.
Task Manager: Visual process control and termination.
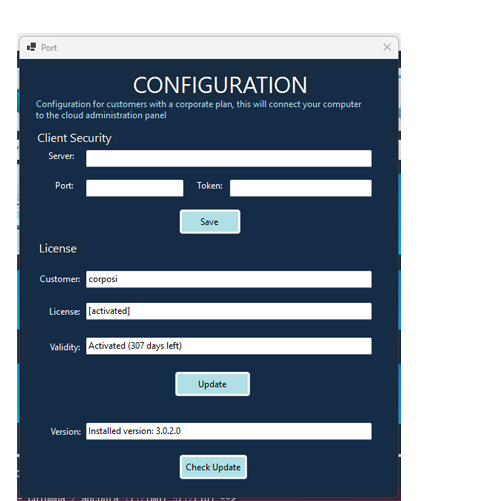
Purpose: Manages licensing and corporate connections.
Corporate Settings: Server, Port, and Token fields connect endpoints to a centralized security panel.
License Section: Displays customer name, activation status, and remaining validity.
Update Control: Allows checking and applying software updates directly from the UI.